Privacy Notice
1. Product scope
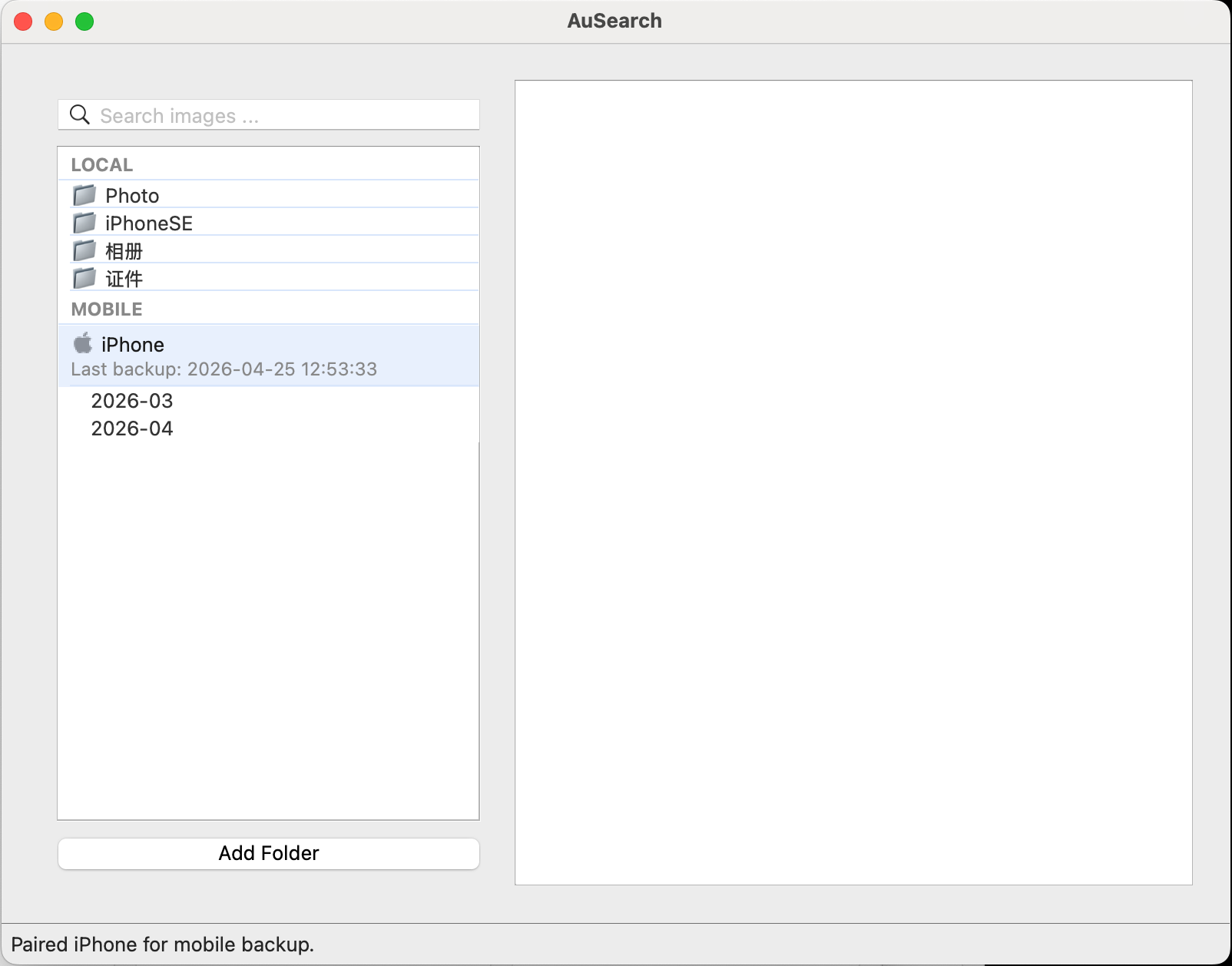
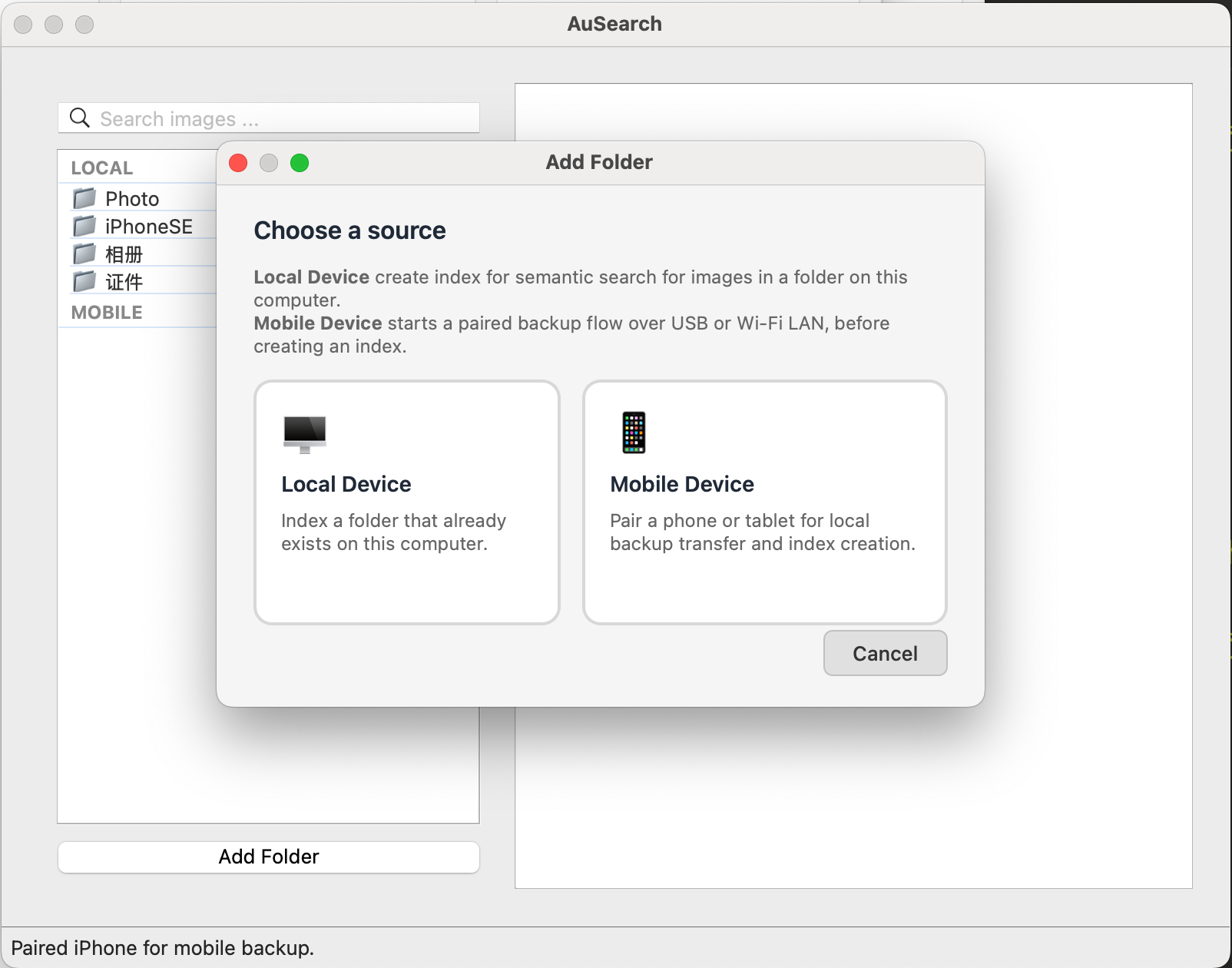
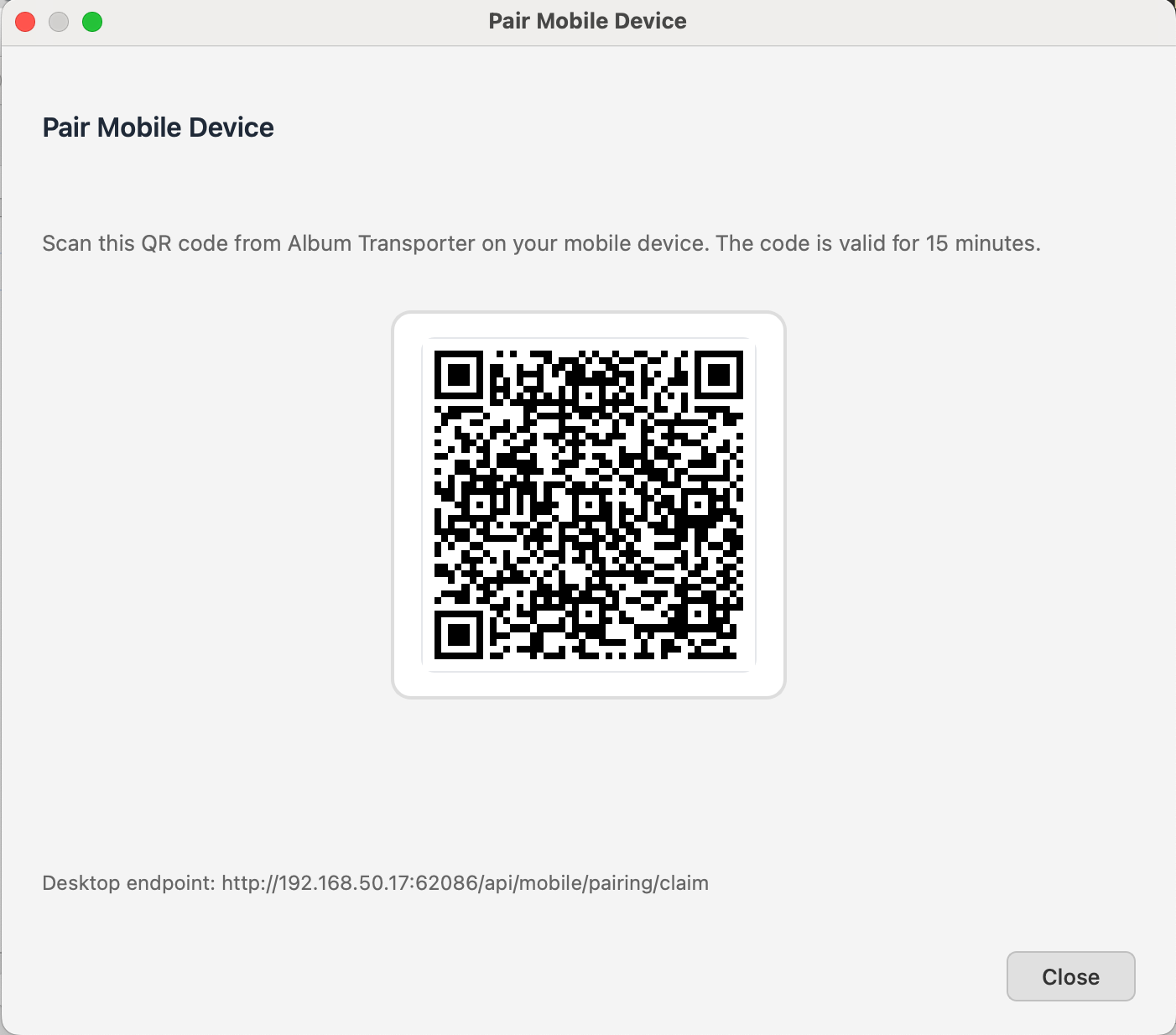
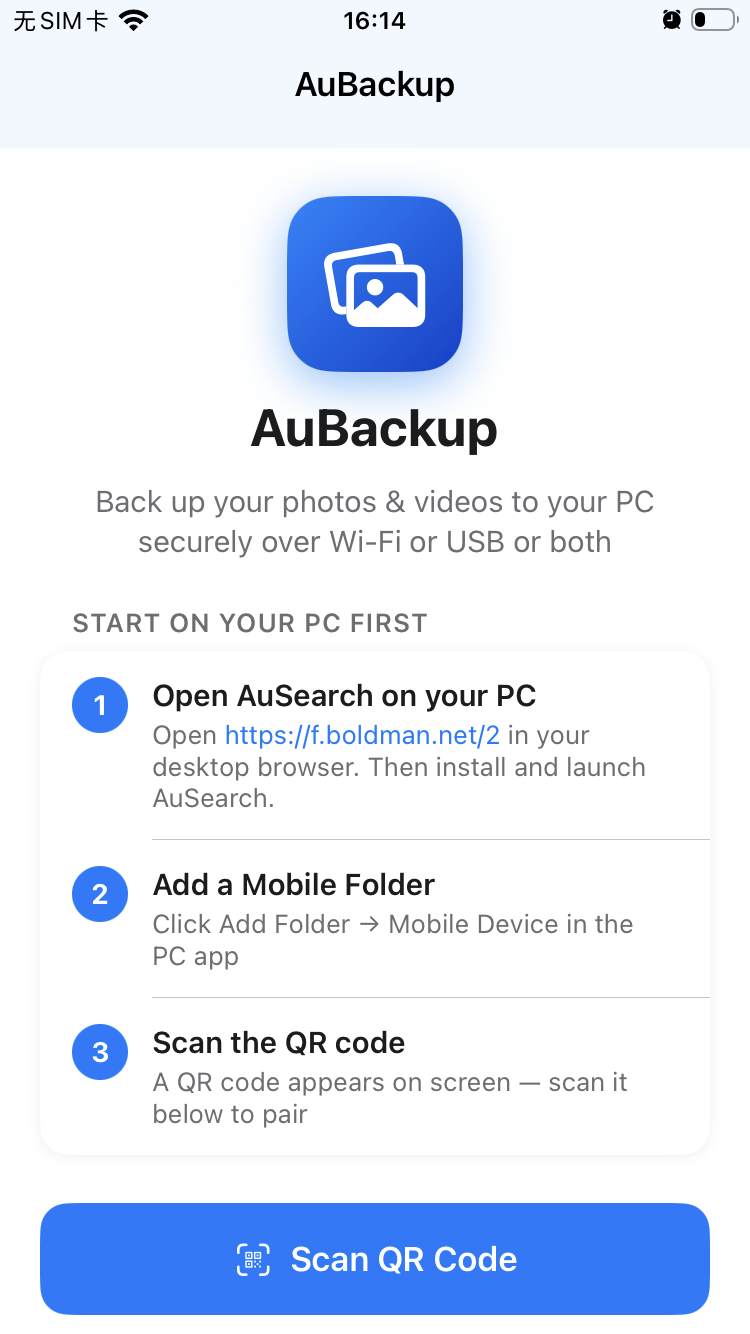
This privacy statement describes AuSearch and AuBackup themselves. It focuses on how the products handle your files, search workflows, transfer workflows, and operational diagnostics.
2. Local-first by design
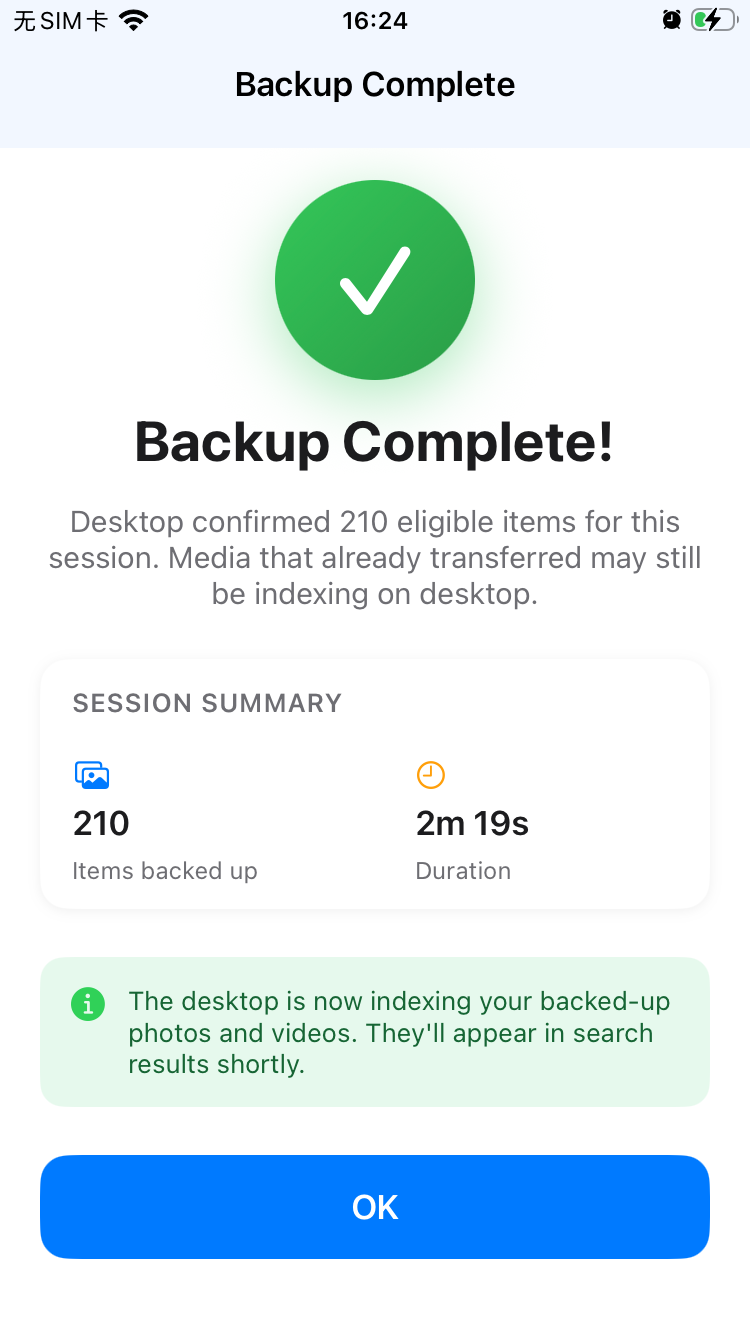
We do not collect your personal files, photos, videos, search content, or other user data for our own servers. AuSearch is designed for local semantic search, and AuBackup is designed for authenticated and encrypted transfer between your devices in a professional manner. Your content is intended to stay under your control.
3. Telemetry and diagnostics
The products may generate limited usage telemetry only for app health maintenance, stability monitoring, and troubleshooting. This is not used to build user profiles, and is never sent to external servers by us.
4. Local AI model use
AuSearch uses open source multi-modal models for local semantic search. Model inference is intended to happen locally for search features. We do not perform hidden training on your content, and your files are not used behind the scenes to train proprietary models.
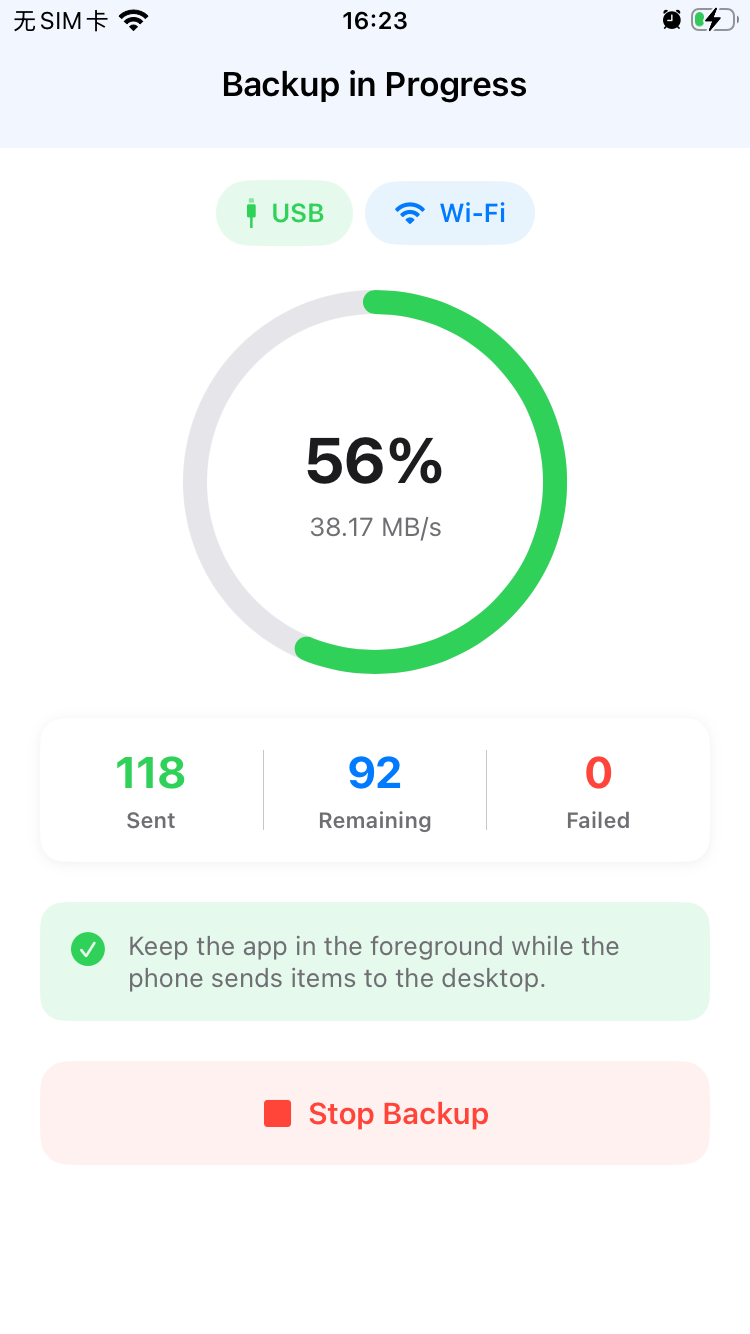
5. Security and transport protection
We value software security. Data transfer paths are designed to use authentication and encryption so that connected devices can verify one another and protect content in transit. Access to local files and device permissions should be limited to what is necessary for search, transfer, indexing, preview, and backup features.
6. Changes
If product behavior changes in a way that materially affects privacy, telemetry, model usage, or security handling, this notice should be updated to reflect that change.